In today’s digital landscape, where cyber threats continue to grow in sophistication and frequency, organizations are facing greater pressure to secure their most sensitive data and critical infrastructure. Among the essential components of a modern cybersecurity framework, Privileged Access Management (PAM) tools plays a central role in protecting privileged accounts, entitlements, avoiding insider misuse, credential theft, and external attacks.
PAM solutions help safeguard high value systems such as servers, databases, cloud platforms, and sensitive information by enforcing strict control, continuous monitoring, and detailed auditing of privileged user activity.
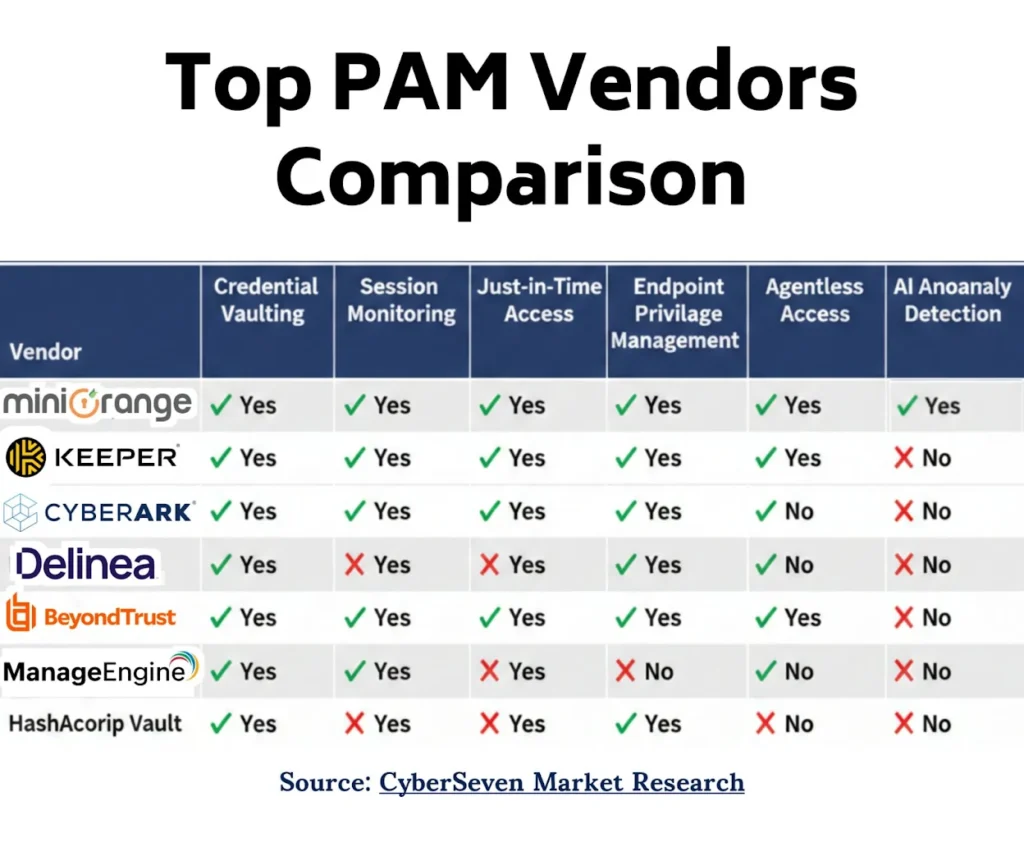
To create this list of top 5 best PAM solutions for large companies, we have carefully compared dozens of PAM solution vendors available in the market, examining their features, benefits, deployment models, innovations, and overall strategic value.

The Evolution of PAM: From Traditional to Intelligent Solutions
The evolution of Privileged Access Management (PAM) has accelerated rapidly in recent years, transitioning from simple password vaulting tools to intelligent, AI-driven security platforms. This shift has been fueled by several factors, including the growing sophistication of cyberattacks, the expansion of multi-cloud environments, stricter regulatory requirements such as GDPR, HIPAA and CCPA, and the increasing need for real-time detection and response capabilities.
Notable trends shaping PAM in 2026 include:
- AI and Machine Learning Integration: Many PAM Vendors are integrating AI-driven security controls, Enabling real-time anomaly detection, automated risk scoring, and faster incident response.
- Cloud Native PAM: Provides scalability, easier deployment, and better alignment with cloud-first strategies.
- Zero Trust and Micro Segmentation: Strengthens least privilege enforcement and reduces lateral movement risks.
- DevSecOps and Automation Support: Enhances CI/CD security and improves operational efficiency through integration with DevOps toolchains.
- User and Entity Behavior Analytics (UEBA): Continuously monitors behavior patterns to detect insider threats and compromised accounts.
- Passwordless and Biometric Authentication: Reduces reliance on static credentials and enables more secure, frictionless access.
Top 5 Leading Privileged Access Management Tools
Here is a well-researched and detailed list by our team of which vendors lead the PAM market in 2026. This leading PAM tools comparison will help you make the right decision based on your organization’s needs. Let’s begin.
1. CyberArk
CyberArk is a leading privileged access management tool available in the market, especially for larger enterprises. It is designed to secure and manage high-risk privileged access across your entire IT environment, including multi-cloud and hybrid setups. It keeps your most sensitive systems safe by securing remote access for employees and unauthorized third-party access.
Key Features:
- Privileged Account discovery:
CyberArk PAM allows users to conduct comprehensive audits to identify all privileged accounts across their IT environment, including admins, executives, service accounts, and machine identities.
This critical step involves mapping the high-risk entitlements associated with each account to ensure complete visibility into who has access to what resources and sensitive data. Automated discovery tools continuously scan cloud platforms, on-premises systems, and hybrid infrastructures to detect shadow accounts and extended privileges. - Granular Access Control:
Granular access control allows giving specific required permissions to users or groups. This works on principle of least privileged, meaning giving permission to only required resources and nothing more. GAC enables strict security for privileged accounts, reducing the risk of insider threats.
CyberArk PAM supports Role-Based Access Control (RBAC), Attribute-Based Access Control (ABAC), Mandatory-Based Access Control (MBAC), Discretionary-Based Access Control (DBAC), and Policy-Based Access Control (PBAC) models, offering flexible and fine-tuned access control across diverse environments. - Just in Time Access Management:
JIT access management is another popular and matured feature of PAM, which delivers time-bound privileged access and removes standing privileges to reduce the risk of misuse. This feature allows granting access for the limited time period required to complete that particular task, and after the task completion, access is automatically revoked.
Also Read: List of Top Just-in-time access management solutions - Privileged Session Monitor and Control:
Admin can enable real-time session oversight with monitoring, alerts, and session recording. This allows protecting the system in real time from any insider threat. The system detects any suspicious activity and terminates the sessions. This feature also makes the organization support compliance and investigations. - Password Vault and Rotation:
Password vault identifies and centrally stores elevated access credentials, reducing security risks. Without these tools, passwords may be insecurely stored, forgotten, or shared inappropriately, leading to potential data breaches.
This feature also allows automated password rotation, which makes all privileged passwords get rotated at a certain interval of time without being known to anyone.
Why it is a top choice in 2026:
CyberArk’s focus on integrating AI-powered threat detection and extensive integrations with various IT ecosystems brings many advanced features to its solution. However, the higher cost and excessive unusable features make it suitable mainly for very large enterprises with complex infrastructures.
2. miniOrange PAM Solution:
miniOrange is a dominant force in the Modern PAM space, continuously innovating to address enterprise security challenges. It is recognized for its unified, scalable and identity-centric PAM platform that helps organizations manage, monitor, and secure privileged credentials across cloud, on-premises, and hybrid environments, making it suitable from mid market to and large enterprises.
With strong applicability across industries such as healthcare, finance, manufacturing, information technology, and more, miniOrange delivers powerful privileged access protection without the complexity often found in enterprise tools.
Additional Capabilities
- Secures privileged credentials across cloud, on-premises, and hybrid IT environments.
- Built to support diverse industry use cases including healthcare, finance, manufacturing, telecom, IT services, and retail.
- User Behavior Analytics: Use AI insights to detect suspicious activity.
- Highly scalable to support SMBs, MSPs managing multiple clients, and large enterprises with complex infrastructures.
- 24×7 support ensures continuous assistance for mission critical environments.
- Agentless architecture simplifies deployment and reduces maintenance overhead.
- Cost effective and customizable to meet specific organizational requirements.
Key Features:
- Eliminates unauthorized access risks with Zero Standing Privileges.
- With full access logs, makes audit processes simplified.
- Automatically rotates all privileged accounts and credentials.
- Flexibility of choosing from SaaS or self-hosted deployment options.
- Empowers users and efficiency, reducing IT workload.
Why it is a top choice in 2026:
miniOrange PAM stands out for its modern identity-first security approach and strong balance of enterprise grade security and ease of use. Its agentless architecture, flexible deployment options, and AI assisted monitoring help organizations manage privileged access with minimal friction. Combined with 24×7 support, multi-environment compatibility, and affordability, it delivers exceptional value for growing businesses, MSPs, and enterprises looking for a modern, scalable PAM solution.
Pricing:
miniOrange PAM pricing is based on admin licenses. The average price starts at $30 per admin per month. This price includes all PAM features and the resources listed in the dashboard. There may also be a one-time setup cost, depending on your infrastructure.
Watch our video on Top 5 PAM solution vendors to get clear understanding
3. ManageEngine PAM360
ManageEngine has its PAM360 privileged access management solution. It is an enterprise-grade PAM solution developed by Zoho Corporation. ManageEngine secures privileged credentials and monitors activity, streamlines privileged access workflows, supports containerized environments and CI/CD pipelines, and easily integrates with SIEM and identity platforms. It also provides robust reporting tools for audits and compliance.
Key Features:
- Privileged password vaulting and rotation
- Session monitoring, approval workflows, and audit-ready reporting
- Granular access control
- Easy integration with SIEM tools, ticketing tools, and other ManageEngine products
Why it is a top choice in 2026:
ManageEngine is a brand backed by the giant Zoho Corporation. They have been in the field of building IT management solutions for over two decades and provide a resilient and robust PAM tool that is trusted by government agencies and leading organizations.
4. BeyondTrust PAM Solution
BeyondTrust Identity Security and Privileged Access Management (PAM) solutions provide a variety of security, service desk, compliance, and industry-specific use cases. Their solution includes several features such as Password Safe, Privileged Remote Access, and Endpoint Privilege Management.
Key Features:
- Allows zero trust remote access to critical systems without exposing privileged credentials.
- Automated password rotation, audit trails, and granular session controls.
- Combines behavior analytics with threat intelligence feeds.
- Allows discovering, assessing, and controlling AI risks as part of a unified identity security platform.
- Seamless integration with existing ITSM tools for advanced workflows.
Why it is a top choice in 2026:
BeyondTrust provides strong security coverage through its advanced threat analytics, zero trust remote access, and powerful session controls. Its ability to manage complex enterprise environments, combined with behavior analytics and integration with major ITSM and security tools, makes it highly reliable for organizations with strict compliance needs.
5. Microsoft PAM Solution
Microsoft PAM is developed to secure Microsoft-centric environments. It secures identity systems like Microsoft Entra ID and Microsoft Purview PAM, which are tightly integrated into the Microsoft 365 and Azure ecosystems. They include features such as credential vaulting, session recording, and workflow automation that are not native to Microsoft’s PAM for external systems.
Microsoft PAM does not have native capabilities to manage credentials or sessions for non-Microsoft platforms like Linux, other cloud providers, or legacy systems. So, if you want to manage a variety of systems that include both Microsoft and non-Microsoft products, it is better to choose other third-party PAM providers like miniOrange or CyberArk.
Key Features:
- Strong security and easy integration with Microsoft 365, Azure, and Entra ID
- Enforces Multi-Factor Authentication
- By enforcing least privilege, it simplifies regulatory requirements
- Reduces the manual overhead of managing administrative roles
Criteria for Evaluating the Best PAM Solutions in 2026
- Security Features: Credential vaulting, password rotation, session monitoring, MFA support, adaptive risk scoring, AI-driven anomaly detection.
- Privileged Account Controls: Management of shared, service, and application accounts, real-time session oversight, session recording.
- Behavioral Analytics: User and entity behavior analytics, risk-based access evaluation, ML-powered threat detection.
- Automation and Orchestration: Automated workflows, password resets, least privilege enforcement, policy-based provisioning.
- Scalability and Cloud Readiness: Native support for multi-cloud and hybrid environments, ability to scale with organizational growth.
- Integration Capabilities: Compatibility with IAM, SIEM, SOAR, ITSM, DevOps pipelines, cloud platforms, and identity providers.
- Compliance and Auditing: Detailed logs, audit trails, regulatory reporting for GDPR, HIPAA, CCPA, SOX, and other standards.
- Usability and User Experience: Intuitive interface, easy onboarding, frictionless authentication methods, streamlined workflows.
- Deployment Flexibility: Options for on-premises, cloud, SaaS, or hybrid deployment models.
- Vendor Support and Reliability: Quality customer support, strong documentation, active community, proven vendor reputation.
Conclusion:
In 2026, selecting the best Privileged Access Management tool involves understanding not only the current technological landscape but also emerging trends and organizational needs.
The softwares listed above, CyberArk, miniOrange, BeyondTrust, ManageEngine, microsoft, offers advance features, AI-driven analytics, cloud-native deployment options, and integration capabilities to meet organizations’ evolving cybersecurity challenges.

Omkar Deo is a cybersecurity and SaaS professional with over six years of hands-on experience in the field. He works closely with modern security solutions and scalable software products, focusing on real-world implementation and business impact. Passionate about emerging technologies, Omkar constantly explores new tools, trends, and architectures to stay ahead in the fast-evolving tech landscape.




